How Can Someone Hack Your Crypto Wallet? 6 Real Attack Vectors in 2026
How can hackers access your crypto wallet? Discover 6 real attack methods in 2026 and learn how to protect your funds with practical security strategies.


Let's rip off the band-aid immediately: the biggest vulnerability in crypto is You. According to Chainalysis, over $17 billion was stolen in 2025, and the scariest part? Most of these attacks didn't exploit zero-day exploits or quantum computing breakthroughs. They exploited something far simpler: trust, urgency, and human error.
One wrong click, one copied QR code, one "customer support" DM, and your life savings evaporate into a blockchain black hole. In 2026, hackers have traded complex code-breaking for sophisticated psychology-breaking hacks. They use AI-generated deepfakes, physical mail campaigns, and sophisticated phishing schemes that empty your assets faster than you can say "seed phrase." Understanding exactly how these attacks work is your only defense. Here are the six most dangerous ways someone can hack your crypto wallet right now.
Malware That Replaces Your Wallet Apps
Forget keyloggers. In 2026, attackers deploy malware like DeepLoad, advertised on dark web forums, that actively replaces legitimate wallet applications on your device with counterfeit versions. When you try to open Ledger Live or Exodus, a fake interface launches instead, politely asking for your seed phrase. By the time you realize what happened, your wallet is empty.
Similarly, the GlassWorm malware now targets macOS users by planting malicious VSCode extensions that scan for browser extension wallets and even attempt to replace legitimate hardware wallet apps like Ledger Live with trojanized versions .
Physical Mail Phishing
Hackers have gone old school, really old school. In February 2026, Ledger and Trezor users began receiving physical letters at their home addresses, complete with fake holographic seals and urgent warnings about mandatory "authentication checks". Scan the QR code inside, and you're on a phishing site that looks exactly like the real thing, begging for your recovery phrase. These letters leverage customer data from past breaches (2020 Ledger hack, anyone?) to target victims with frightening accuracy.
Supply Chain Attacks on Official App Stores
You think downloading from the official app store keeps you safe? Think again. In January 2026, Trust Wallet's Chrome extension was compromised after attackers obtained GitHub secrets and a Chrome Web Store API key, pushing a malicious update that stole $8.5 million from 2,500 wallets. Meanwhile, the Linux Snap Store hosted malicious apps disguised as Exodus and Ledger Live, stealing seed phrases from unsuspecting users. Yes, even "official" sources can be weaponized if you trust only official sources without additional validation.
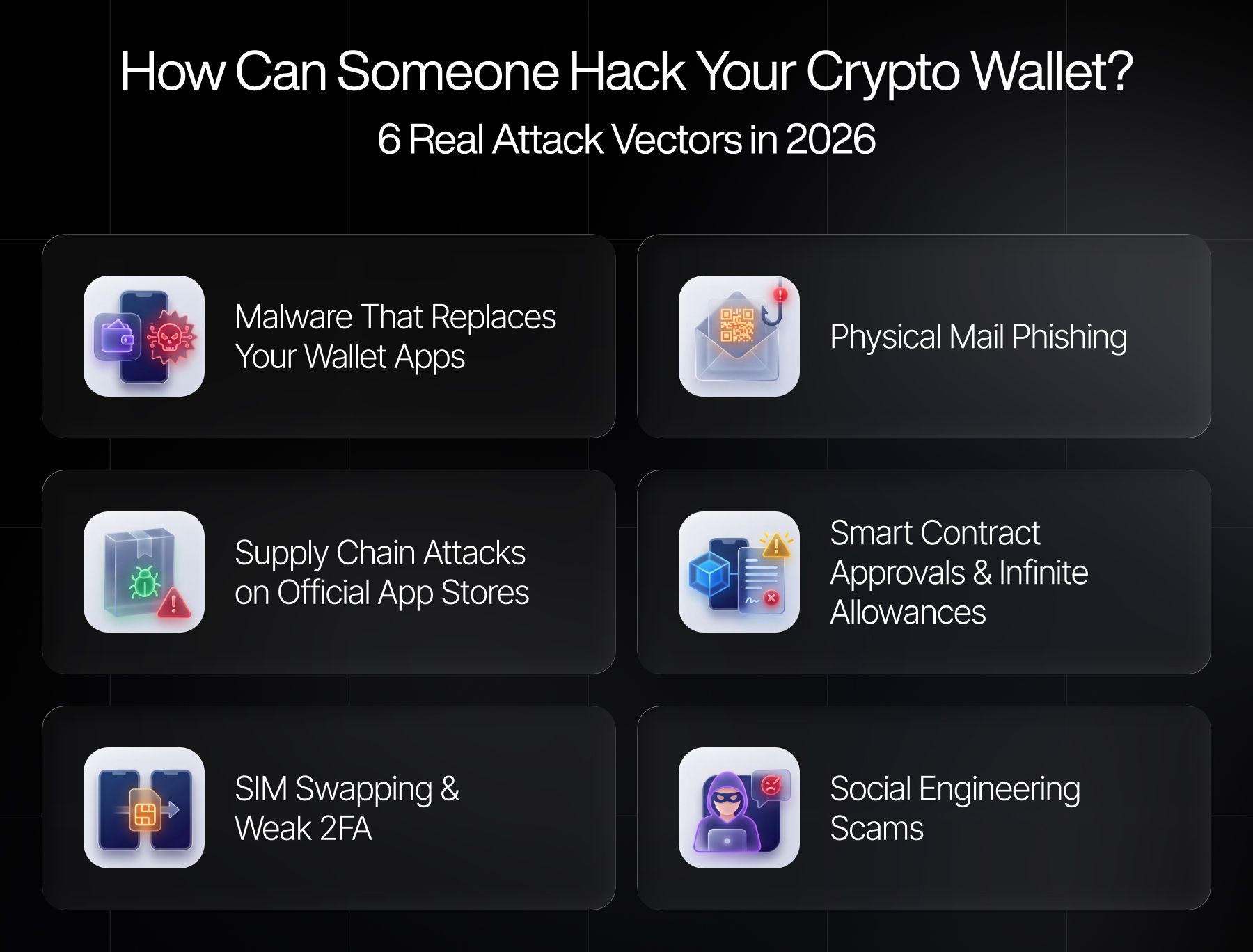
Smart Contract Approvals and "Infinite Allowances"
You connect your wallet to a shiny new DeFi protocol. It asks for permission to spend your USDC. You click "Approve" without a second thought. Congratulations, you've handed the attacker a license to drain your entire balance. Malicious dApps request "unlimited approvals," then slowly siphon funds over time without you noticing. Tools like Revoke.cash exist for a reason: because these approvals are ticking time bombs.
SIM Swapping and Weak 2FA
Your exchange account is secured by SMS two-factor authentication. Great. Except a hacker calls your mobile carrier, pretends to be you, and convinces them to swap your SIM to a new phone. Now every "reset password" link lands in their inbox. SMS 2FA is not security; it's a polite suggestion. Use hardware security keys (YubiKeys) or authenticator apps, or accept that your account is rent-controlled by hackers.
Quick For Instance: the $284 Million Social Engineering Masterclass In January 2026, a single victim lost $284 million: not to code, but to a phone call. An attacker impersonated Trezor support, convinced the user to reveal their recovery phrase, and walked away with 1,459 BTC and 2.05 million LTC. The stolen funds were immediately swapped to Monero, vanishing into privacy coin oblivion. This single attack accounted for over 70% of January's total crypto losses.
Here is the unvarnished reality of 2026: your crypto wallets will never be "hacked" in the Hollywood sense. No one is cracking SHA-256 in a basement. They're tricking you. They're mailing you letters. They're replacing the apps and spoofing the verification processes you trust.
So, what to do? In crypto, security is treating every interaction as hostile. Never enter your seed phrase anywhere except your hardware device. Assume every DM and every call is a scam until proven otherwise. Send test transactions, revoke approvals and for the love of Satoshi, throw that "digital backup" of your seed phrase in Google Drive directly into the trash.
Most losses in crypto don’t come from hacks — they come from mistakes. Brighty App helps you simplify the way you manage and spend crypto, so there’s less room for error.